
Beyond the Buzz: AI Security Unpacked
Cloud Security - 2 min read
This assessment focuses on application-level vulnerabilities, including SQL injection, cross-site scripting, logic flaws, authentication bypass, and more. Following OWASP guidelines, Stratum employs a combination of automated and manual testing techniques tailored to the application's risk profile and technology stack. Our assessments are conducted by highly skilled professionals, ensuring thorough and precise identification of security flaws.
| Basic |
|---|
|
Designed for basic security assessments. |
| Automated security scan |
| Basic reporting |
| Web apps for up to 2 user roles |
| Automated security scan |
| Advanced Vulnerability reporting |
| Manual security testing |
| Web apps up to 4 user roles |
| Complex workflows |
| Time boxes assessment or full pen test options |
| Standard |
|---|
|
Standard pen test for small to medium size organizations. |
| Automated security scan |
| Basic reporting |
| Web apps for up to 2 user roles |
| Automated security scan |
| Advanced Vulnerability reporting |
| Manual security testing |
| Web apps up to 4 user roles |
| Complex workflows |
| Time boxes assessment or full pen test options |
| Ultimate |
|---|
|
Pen tests that include everything. |
| Automated security scan |
| Basic reporting |
| Web apps for up to 2 user roles |
| Automated security scan |
| Advanced Vulnerability reporting |
| Manual security testing |
| Web apps up to 4 user roles |
| Complex workflows |
| Time boxes assessment or full pen test options |
Stratum's Penetration Testing services assess the security posture of your infrastructure against both external and internal threats. We thoroughly identify your external and internal attack surfaces using the same tools, techniques, and tradecraft used by real-world attackers. By simulating real-world threat actors, we identify weaknesses in your external and internal infrastructure by animating your entire security stack. Our detailed analysis offers actionable recommendations that will enhance your network security posture and reduce the likelihood of a successful breach. All penetration testing services can be used to satisfy penetration testing requirements for various compliance frameworks such as PCI-DSS, SOC2, HIPAA/HITECH, ISO 27001, etc.
| Basic |
|---|
|
Basic compliance-based security assessment. |
| Full port scan – 65k ports |
| Service discovery & identification |
| Automated vulnerability scanning |
| Analysis and Reporting |
| Manual false positive/negative analysis |
| Selective vulnerability exploitation |
| Open Source Intelligence (OSINT) assessment |
| AI-powered domain name discovery & attribution |
| Attack surface discovery |
| External asset identification |
| External user password strength assessment |
| Email-based Phishing attack targeting users |
| Dark web data search |
| Standard |
|---|
|
Standard pen test for small to medium size organizations. |
| Full port scan – 65k ports |
| Service discovery & identification |
| Automated vulnerability scanning |
| Analysis and Reporting |
| Manual false positive/negative analysis |
| Selective vulnerability exploitation |
| Open Source Intelligence (OSINT) assessment |
| AI-powered domain name discovery & attribution |
| Attack surface discovery |
| External asset identification |
| External user password strength assessment |
| Email-based Phishing attack targeting users |
| Dark web data search |
| Ultimate |
|---|
|
Full scope external penetration test with skilled tester using all available means to compromise the target |
| Full port scan – 65k ports |
| Service discovery & identification |
| Automated vulnerability scanning |
| Analysis and Reporting |
| Manual false positive/negative analysis |
| Selective vulnerability exploitation |
| Open Source Intelligence (OSINT) assessment |
| AI-powered domain name discovery & attribution |
| Attack surface discovery |
| External asset identification |
| External user password strength assessment |
| Email-based Phishing attack targeting users |
| Dark web data search |
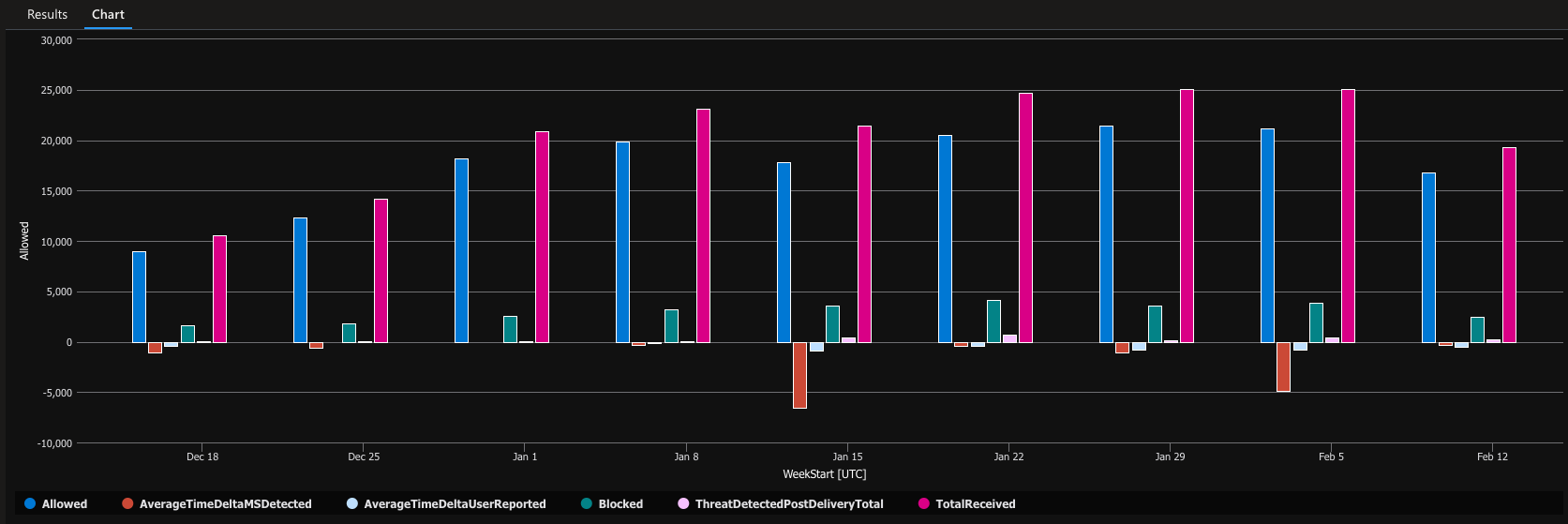
Ensure the security of your cloud environments with our detailed Cloud Security Assessments service. We evaluate the security of your cloud infrastructure, applications, and services across AWS, Azure, M365, and Google Cloud platforms. Our assessment covers identity and access management, data encryption, compliance, and configuration management. We provide a detailed report highlighting vulnerabilities and offering practical solutions to secure your cloud assets.
We offer staff augmentation services emending our security professionals into your organization. We can help to provide app, cloud, and network security support integrating with your organization’s security team.
Genuine security inside an open-source environment.
Stratum provides services to clients world wide. Our list of customers include large multi-national enterprises to small start-ups in numerous industries including finance, insurance, retail, hospitality, health care, government, technology, energy, and telecommunications.

Founder and Managing Principal

Principal Security Consultant

Principal Security Consultant

Open Positions

Principal Security Consultant

Project Manager

Security Consultant

Business Development Manager and Recruiter

Security Consultant

Security Consultant

Security Consultant

Project Manager

Senior Security Consultant

Senior Security Consultant

Senior Security Consultant

Security Consultant

Security Consultant

Security Consultant

Senior Security Consultant

Security Consultant

Security Consultant

Security Consultant

Security Consultant

Security Consultant

Security Consultant

Security Consultant

Account Director

Security Consultant

Security Consultant

Managing Partner and VP

Managing Partner
Focus completely on the person you're talking to without getting distracted. Don't worry about agreeing or disagreeing, just be curious and try to understand their point of view by listening carefully.
When communicating, it's important to be clear, honest, and on the same page with everyone. This means explaining things well, keeping people updated, and ensuring everyone understands, whether with our team, clients, or partners.
We check our egos at the door and prioritize collective success over individual recognition. At our core, we understand that true greatness is achieved when we work together selflessly, with a shared commitment to the mission and our values.
It's our golden rule. It's about honoring commitments, following through on promises, and holding ourselves accountable. We believe in the power of integrity and reliability, ensuring that our actions always align with our words.
A relentless pursuit of personal and professional growth and development. We embrace challenges, seek feedback, and continuously strive to become the best versions of ourselves. At our core lies a commitment to lifelong learning and a dedication to constant improvement in every aspect of our lives.

Cloud Security - 2 min read
4 min read
Pentest - 8 min read
You can select multiple options depending on your needs.
A: We certainly can! Stratum offers tailored packages precisely for these scenarios, providing feature release testing aligned with your release cadence. If you wish to test specific application features before they go live in production, Stratum has you covered.
A: Our pen testing reports will meet PCI-DSS, SOC 2, ISO 27001, HIPAA, and other industry standards.
A: Yes. Stratum Security not only provides a comprehensive report with step-by-step instructions on reproducing the findings, but we also schedule meetings with you and your team to ensure that each vulnerability is thoroughly understood and to provide proper guidance for remediation.
A: On average most tests take from 1-2 weeks depending on the size and complexity of your appplication or environment.
One aspect we take immense pride in is our ease of collaboration! We go the extra mile by setting up Slack or Teams channels for you to directly communicate with us during testing. This grants you direct access to the tester. Moreover, we are easily reachable by phone and email!
A: Stratum can conduct a secure code review on any application source code utilizing both manual and automated approaches. Our testers were formerly developers who transitioned into the realm of application security.
With access to the source code, we can pinpoint vulnerabilities in the coding structure and provide a comprehensive report. Additionally, Stratum offers services for Software Composition Analysis of third-party software, identifying risks in both direct and transitive dependencies.
A: Yes, with every Stratum Security Pen Test 1 retest is included. This will help to verify findings are fixed and close them out in the final report.
A: At Stratum, we employ a blend of manual and automated testing techniques. While scanners are valuable, manual exploitation of vulnerabilities often yields superior results, uncovering more high and critical vulnerabilities than any scanner can.
The human touch affords us control over the testing process, enabling us to attack it in a manner akin to a real hacker's approach.
A: Stratum offers staff augmentation services! We can embed application security experts, cloud security experts, and network security experts in your organization.
From program building to pen testing Stratum can handle all your security needs from within your organization.
We use cookies to enhance your experience. By clicking ¨Accept all cookies¨or selecting ¨Necessary Cookies¨, you agree to our privacy policy.